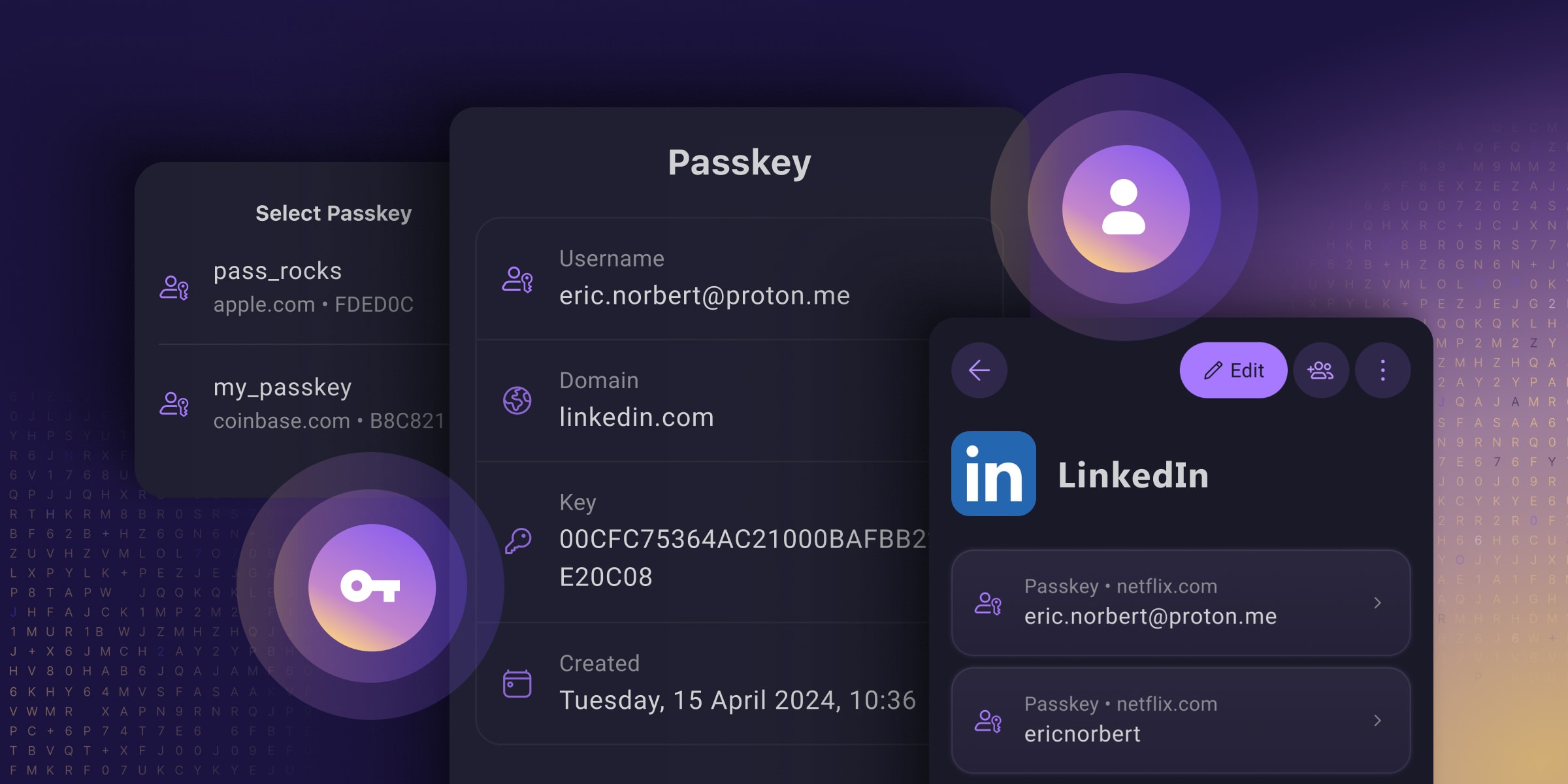
Passkeys are an easy and secure alternative to traditional passwords that can help prevent phishing attacks and make your online experience smoother and safer.
Unfortunately, Big Tech’s rollout of this technology prioritized using passkeys to lock people into their walled gardens over providing universal security for everyone (you have to use their platform, which often does not work across all platforms). And many password managers only support passkeys on specific platforms or provide them with paid plans, meaning you only get to reap passkeys’ security benefits if you can afford them.
They’ve reimagined passkeys, helping them reach their full potential as free, universal, and open-source tech. They have made online privacy and security accessible to everyone, regardless of what device you use or your ability to pay.
I’m still a paying customer of Bitwarden as Proton Pass was up to now still not doing everything, but this may make me re-evaluate using Proton Pass as I’m also a paying customer of Proton Pass. It certainly looks like Proton Pass is advancing at quite a pace, and Proton has already built up a good reputation for private e-mail and an excellent VPN client.
Proton is also the ONLY passkey provider that I’ve seen allowing you to store, share, and export passkeys just like you can with passwords!
See https://proton.me/blog/proton-pass-passkeys
#technology #passkeys #security #ProtonPass #opensource

I didn’t mention it because the comment is not about that (?). But it does worry me. This is why I have 2FA with my authentication/password manager, and do make sure to remember my password to that, because it is the one service remembering all my passwords, TOPTs and passkeys.
I agree that it is less secure, but it’s a necessary evil. Furthermore, it’s mandatory. Security and convenience are always at odds. Passkeys theoretically hit a sweet spot of both qualities. But they come with a higher potential for a possible theoretical lockout.
Let’s assume you have an email, you access this via a passkey authenticator that remembers all your passkeys. To access the authenticator you have to provide either a fingerprint on your phone or a password + OTP to your email. This is a system on potential lockout.
If your phone is stolen or destroyed, now you can’t use the phone to access your email, nor login into your email to verify your access to the passkey authenticator. Now you are locked out of your entire digital life. This is not a rare occurrence, it happens everyday. The only reason it’s not catastrophic is because some part of the chain is password only, and the person remembers the password. Or the second factor is on a trusted third party (like cellular carriers reinstating phone numbers via ID check).
Just like welding all doors and windows shut, yes it is more secure, but you also locked yourself out of the house. You want to still be able to enter the house.
But they don’t. I think this is where your confusion is. I think you’re worrying over a problem that doesn’t exist.
It does not.
If you’re scared of losing both your device and your recovery codes for TOTP, to the point that you store those in your password manager, and you’re happy with that solution, then just store your passkeys in your password manager. Thats literally what this post is about.
And even if you store your passkeys on device for an iPhone for example, they’re stored in your iCloud Keychain which can be recovered if you lose your device. Theres also just nothing about Passkeys that prevent a service from offering an account recovery service.
If you’re already using 2FA, then Passkeys do not pose any additional risk to being “locked out” of your accounts. They actually have less risk usually.