Lists of things not to do:
- (NEW!) Go through airport security with an encrypted laptop, sensitive information and free conference stickers showing your affiliations as an activist. Let airport security confiscate your laptop. Airport security drugs and wrenches you. You give them your laptop password. The police arrests you based on suspicions of terrorism.
Except when your drive is encrypted you can easily destroy its contents. Let’s say you’re DorkPirate1337 who happens to care about their opsec; you
luksEncryptyour drive and have a simple script that runs when a specific USB key is disconnected, triggersluksErase, and thenpoweroffs. Voila, when the school principal snatches your unlocked laptop while you’re in the lib, all your pirated hentai becomes permanently unaccessible whether you give up the password or not. [Edit: the USB key is strapped to your wrist]Note: luks uses 2 encryption keys, where one is randomly generated and encrypts the actual data, and the second one is given by the user and encrypts the first one;
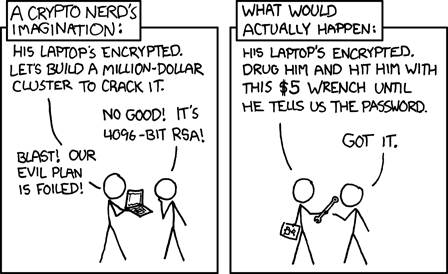
luksErasedestroys the luks header containing that first keyNot that other means of accessing the passwords aren’t worth considering, but in the real world, it takes a lot more for someone to actually coerce your password from you than to use unencrypted storage.
I generally like xkcd, but this is a harmful trivialization of the value of encryption. In the real world, anything that isn’t encrypted is negligent as hell. There’s no valid reason not to do it, with maybe the exception of a thumb drive you’re sharing across a computers you don’t control and are clearly aware is not secure.
Safe in what context ?
If the drive is mounted and data accessible, in case your computer is compromised by some kind of malware, well, the data will be easy to exfiltrate. Now, if the computer is turned off or the drive unmounted, that’s what encryption comes in to protect it.
So, basically, encryption will protect the data in case of physical theft of the drive or in case of remote hacking if the drive is un-mounted.
Safe in the context of someone stealing the hard drive and look through private photos and stuff by plugging the drive into another device.
In that case, without encryption, your safety is zero. That’s the exact scenario that full-drive encryption was designed for.
Well… shit. Thank you for your great advice. I’m gonna look for how I can secure my data.
Out of curiosity what sort of safety did you think an unencrypted hard drive had?
I mean no offense and I think it’s a perfectly fine question to ask, I just want to understand what you expected.
I had the expection that Linux is already set up as a multi-user environment and has that feature built in.
Of course that “isolation” of data, as I had it in my mind, wouldn’t be really secure, but it doesn’t have to be that for me. I just don’t want anyone to access it easily.
Perhaps it’s useful to provide some clarification here. As the other user stated, Linux is set up for multi-user setups and provides logical protection, but you seem to misunderstand how operating systems and file permissions work.
If someone steals your unencrypted hard drive and boots into their own operating system, they are able to circumvent all access control and permissions on your hard drive. This is because when they mount your hard drive your operating system isn’t running; they’re simply reading the stored data, so the access control and permissions set up by your operating system don’t mean anything. This happens with ALL operating systems (Linux, BSD, Windows, MacOS, etc.). Logical protection like access control is only useful while the OS is running, and it cannot help otherwise.
This is why encryption is important, because it prevents unauthorized access when the OS isn’t running. If you’d like to see just how easy it is to access unencrypted data, make a live USB and boot into it on any unencrypted computer (assuming you have permission to do so if you don’t own the computer). You don’t even need to extract the hard drive in most cases to read file contents, you can simply boot into a live USB. The only situation where this isn’t the case is when USB booting is disabled in the BIOS and the BIOS is password protected, but you could always just remove the CMOS battery to clear the settings to bypass the BIOS password anyway.
Unencrypted data will always be trivial to retrieve when the attacker is allowed physical access to your computer.
Simplified, there’s two layers to data protection, physical and logical. Linux or basically any correctly configured modern operating system provides logical protection, i.e. access under the running OS is only granted to authorized users. Granted you can still put holes in here, e.g. a webserver is misconfigured and allows access to any user to all files it can read. However, from the OS perspective, everything is fine, as the webserver can still only read what it’s allowed to.
Data encryption protects data at rest, i.e. when no operating system enforcing the logical protection is running. The case has already been described so I’m not gonna repeat that here.
It’s important to understand that in general, these two measures are completely seperate from each other. Device encryption won’t help against logical attacks, and logical protection won’t help against offline attacks. You need both if you can’t rule out an attack vector completely (i.e. your server sits in a secure safe that can’t be opened by anyone not authorized to, then encryption might not be necessary).
No poorly not. Just as Windows by default. Systemd-homed is a solution for that but afaik its questionable if its ready. Would be great if Distros like Fedora shipped it by default.
An encrypted system rather than an encrypted user partition is still necessary, because attackers could replace system files or simply add a service that uploads your stuff somewhere, or manipulate sudo, or log your password etc.
Now we all want to know if you have child porn
“You must be a criminal if you have curtains”
Wtf, no?!
If I had CP, I wouldn’t ask publicly and make myself vulnerable.
I just don’t wanna have anyone snooping around my stuff, just as everyone else.
You’re using HTTPS, do you have child porn?
Or a sex tape.
Maybe he has yours?
deleted by creator
If the device get stolen, your drive and its files can be easily read.
Other attacks like malware or ransomware are almost the same if the drive is encrypted or not.
Disk encryption is important for laptops and phones because these devices are frequently stolen. For desktop or servers is still good idea, though.
Thanks a lot for your answer. How would you encrypt a server? Typing a password every time it boots isn’t possible for me, since I would need a monitor for my headless server.
That’s why it’s not always an option.
Some servers have some kind remote console hardware, with their own security issues.
Your “threat model” is important too. Do you expect that server to get stolen? If it happens, is there critical data that should not leak?
Maybe you need to encrypt a directory, and not the whole drive.
My threat model isn’t high. Just normal stuff everyone has, but that would be disadvantagely if someone else got them.
It’s more if a precautionary measure. It doesn’t have to be super safe, but better than nothing.
Is this for your home? If it is, you don’t really have to worry about someone stealing your desktop. If someone breaks into your home, they’re looking for quick cash and jewelry and TVs. They’re not going to bother stealing your server to dig through files for something usable.
I’ve had quite a bad experience with police for example.
30 cops raided my home because of something trivial (I ordered a bit of non-psychoactive CBD-weed, which is, even in the most restrictive country you can imagine, ridiculous).
Of course, I got the whole experience-pack, including strip searches and confiscating all electronics.
Even though I believe them getting hold of any data wouldn’t have changed much, I’m still glad I had my devices encrypted.
Just knowing they didn’t see my cringy pictures of my teeny-me, where I discovered Snapchat filters, is a big relief. 😅
Yeah… that traumatized me a bit and maybe that’s the reason I’m worrying.
Also, you could never know what will happen in the future. Maybe my GF will turn crazy tomorrow and use those embarrassing pictures against me. Who knows?
I believe everyone should use encryption, even if they don’t have much to hide…
Oh that’s a really good point. Don’t trust the cops, keep everything encrypted.
Way safer in those situations.
You can use SSH for unlocking: https://www.cyberciti.biz/security/how-to-unlock-luks-using-dropbear-ssh-keys-remotely-in-linux/
Either self-encrypting drives (if you trust the OEM encryption) or auto-unlock with keys in the TPM: https://wiki.archlinux.org/title/Trusted_Platform_Module#Data-at-rest_encryption_with_LUKS
One option may be a hardware security key. Here is an example: https://www.endpointdev.com/blog/2022/03/disk-decryption-yubikey/
If Windows, use BitLocker.
If Linux, use LUKS but you need to enter the passphrase at boot, you can securely put the key in TPM2 I think (à la Windows) but it may be complicated to setup, or just seal the phrase in TPM2 but if you boot on grub you can break grub and replace init with a shell in boot option and have access to the system I think :-/ but a simple crackhead thief would not understand that.
You can also have the key on a USB key, but if on the server and the server get stolen, it’s useless. You can setup a “anywhereUSB” and have your USB key in another room/place, etc, there is others possibilities.
I wanted to unlock with bluetooth but having the bluetooth HW driver and stack in initramfs was nightmarish a little bit :-/
I use Luks/Tang to unlock the server at boot from another computer that is always on too. If that one is down I’ll need to type it or power the other PC on, but otherwise it auto decrypts for me as long as I’m on the same network.
You are relying 100% on physical security. If nobody can take your drive or physically operate your computer, it is safe.
If I could boot a USB stick on your machine, or pull the drive, accessing your data would be trivial.
Somebody can take your disk, easily mount filesystem, and read everything.
If the risk of physical data theft is high, your data is at risk. If the risk of physical access to you machine is rather low, encryption might actually increases the risk of losing your data simply by the chance of losing the means to access your data (forgotten passphrase, lost hardware key…).
It might also be harder to recover picies if the hard drive fail partially. However, many use SSD now, might be a different story there.
I think you mean my data.
our data
I like your thinking, comrade
An encrypted hard drive means that someone cannot physically steal your hard drive and read its contents.
Encryption-at-rest is generally moot against RCE exploits, because your OS will happily decode files that your programs have permission to read.
That said, on modern systems, encryption is cheap. So set it up if you can.
Edit: I replied to the original post.
Community in the text?
Crosspost. Click on it and you’ll land on my original post.
I didn’t want to duplicate it. You can always suggest me how to make the crosspost more visible, I just did it how my client set it up for me.
deleted by creator